- Critical Thinking - Bug Bounty Podcast
- Posts
- [HackerNotes Ep. 165] Protobuf Hacking, AI-Powered Bug Hunting, and Self-Improving Claude Workflows
[HackerNotes Ep. 165] Protobuf Hacking, AI-Powered Bug Hunting, and Self-Improving Claude Workflows
Today, we are digging some protobuf stuff, and also talking about the current debate about AI finding bugs and how to use it properly
Hacker TL;DR
Protobuf parameters on Google are an underexplored attack surface. Claude excels at decoding and re-encoding them
Login CSRF chained with browser permissions (mic/camera) can escalate to full surveillance of victims
Add a self-improving loop to your Claude.md file so it learns from mistakes and saves tokens over time
Models now score ~69% on CyberBench. AI-assisted hacking is no longer hype; it's producing real bounties

Today's Sponsor: Check out ThreatLocker Ringfencing https://www.criticalthinkingpodcast.io/tl-rf
In the News
BB Scope Major Update - @sw33tLie shipped a big upgrade to BB Scope, now with the ability to dump your HackerOne reports via a new pull request, useful for feeding context to AI tools
Caido Skills for Claude Code - Caido officially released a Claude Code skill with SDK integration for searching HTTP history, adding findings, editing requests, and managing match-and-replace rules
Matt Brown Goes Full-Time - @nmatt0 left his job to go full-time into hardware hacking, pentesting, and content creation. His YouTube channel is the go-to resource for IoT device hacking
Protobuf Hacking on Google
Justin has been finding consistent success targeting protobuf-encoded parameters across Google's attack surface. Many parameters are base64-encoded binary protobuf structures that most hunters skip, either assuming they're signed or simply not wanting to deal with the complexity.
How Protobuf Encoding Works
Each field in a protobuf message is encoded with a single byte containing three pieces of information:
Bits 0-2 (Wire Type): Defines the data type like varint, length-delimited string, fixed-size integer
Bits 3-6 (Field Number): The index of this field in the protobuf schema
Bit 7 (Continuation Flag): Indicates whether the metadata extends into the next byte
Without the .proto schema definition, you won't get field names, only field numbers and values. But by decoding nested protobuf structures, you can identify IDs, strings visible in the UI, and internal references that unlock new attack vectors.
So you can use Claude to decode protobuf blobs. It handles nested structures, identifies checksums, and can generate Python scripts to re-encode modified payloads. Justin built a Caido convert workflow to do inline protobuf decoding, which he'll share on the Discord.
We do subs at $25, $10, and $5, premium subscribers get access to:
– Hackalongs: live bug bounty hacking on real programs, VODs available
– Live data streams, exploits, tools, scripts & un-redacted bug reports
Login CSRF + Browser Permissions = Surveillance Chain
Justin shared a high-impact chain he's been reporting successfully across multiple targets:
Login CSRF into the attacker's account on the target application
CSRF the audio recording endpoint to start capturing the victim's microphone
The application transcribes the audio and uploads it to the attacker's account
If the victim has previously granted the site microphone permissions (a domain-level browser setting), this requires zero user interaction. The attacker can silently record and exfiltrate audio.
Browser permissions are scoped to the domain, not to the account. So a login CSRF effectively hijacks those permissions.
Iframe Permission Delegation
Check the allow attribute on iframes. If a parent page delegates permissions like microphone, camera, or display-capture to an iframe you can control, you may be able to abuse those permissions from a third-party context within a trusted top-level page.
AI Hacking Debate: Skill Gaps and False Positives
Can anyone just spin up Claude Code and start finding bugs nowadays ?
What AI Unlocks
Claude Code + xssdoctor found a high/critical on a major company by testing survey endpoints, the kind of boring functionality experienced hunters habitually skip
BusFactor had Claude find a high on a program paying $8K for highs, one bug pays for three years of usage
The gap between technical and semi-technical users has shrunk dramatically, but it hasn't disappeared
Where Human Expertise Still Matters
False positive triage: When Claude says "CRITICAL FINDING," there's roughly a 20% chance it's actually valid. Knowing that a wildcard CORS isn't exploitable or that a finding is a medium rather than a critical requires real security knowledge.
Validation complexity: Even experienced hunters need time to fully understand and validate the unusual bugs AI discovers
Context and judgment: Setting up infrastructure, understanding scope, and knowing what's worth reporting still requires a hacker's intuition
The Self-Improving Claude.md Trick
Joseph shared a practical tip for leveling up your Claude Code setup:
Add this to your CLAUDE.md:
Anytime I get frustrated, anytime I have to re-explain something you didn't understand, or anytime you try a command and it fails repeatedly, add that lesson to the Applied Learning section in your CLAUDE.md.
This creates a self-improving loop: every session makes the next one better. Claude stops wasting tokens on repeated mistakes and learns patterns specific to your workflow, like where session files are stored or which commands work on your system.
Discord Bot for Remote Hacking
Instead of using Claude RC (which doesn't support --dangerously-skip-permissions), Joseph built a Discord bot that acts as a remote Claude Code interface:
Each new task spawns a Discord thread as a session
Tool calls are displayed with diff-formatted code blocks (green for additions, red for removals)
Supports voice messages and attachments for input
Includes a
--resumecommand at the top of each thread for jumping back into sessions from a VPSActs as a DevOps engineer on speed dial — validate findings, check logs, host files, all from a phone
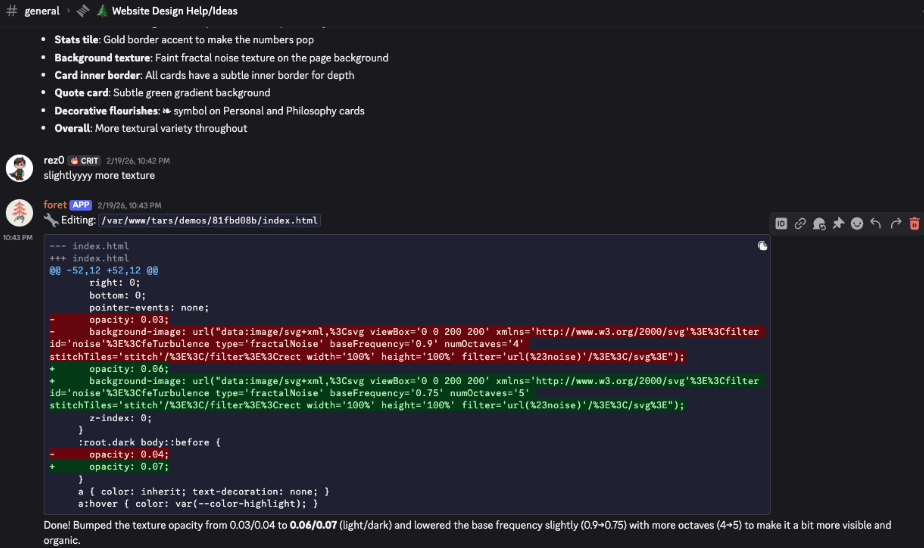
The Discord Bot
Resources
BB Scope - Dump scope and reports from HackerOne/Bugcrowd with API key support
Caido Skills - Official Claude Code skill for Caido proxy integration
Matt Brown's YouTube - Best hardware hacking content on YouTube
Matt Brown's Courses - Digital Signal Analysis for Hardware Hackers ($200) and Beginner's Guide to IoT Hacking ($50)
MDN: iframe allow attribute - Documentation on permission delegation to iframes
Anthropic Privacy Settings - Disable training on your data before feeding reports to Claude
That's it for the week, keep hacking!
